Secure document destruction is imperative to ensure the safety and security of an entity’s information. Breach of the protocol can be catastrophic to both the entity and its business associates. Secure destruction of documents must be done accurately, thoroughly and a verifiable chain of custody is required.
Secure Destruction is Complicated by Wet, Moldy or Contaminated Documents
While secure document destruction must be performed with acute accuracy, protocol becomes complicated when documents have become wet and mold growth has occurred. When paper becomes wet or damp, it often completes the equation to produce mold; moisture + warmth + food. In this case, the food is paper. The presence of mold will create an unsafe environment for those handling the documents. Even if records were once wet but have dried, mold can exist. Employees that are handling the documents or trying to shred them can be exposed to airborne mold spores.
The onset of the mold is a major concern in the secure destruction industry. Some people will have an allergic reaction. Some molds can be toxic. Workers should wear masks or respirators and disposable gloves when working with records containing mold (and have the proper training required by OSHA). There is tremendous litigation over mold in the workplace. An employer has a legal responsibility to forewarn employees of the dangers of being exposed to mold, to train the workers on how to work with mold and to provide the appropriate personal protective equipment (PPE).
Many document destruction companies do not accept wet, moldy or contaminated items. BMS CAT specializes in destroying these types of documents. We come to the customer site, inventory and remove contaminated and wet documents. A detailed inventory list is provided and our proprietary web-based inventory system is compliant with the latest industry regulations including HIPAA, FACTA, HITECH, GRAHM-LEACH-BLILEY, State Regulations and Federal Regulations.
Destruction Techniques
The Federal regulatory compliance laws define the acceptable methods of destruction as shredding, pulverizing or incineration. Federal Standards & the Department of Defense document “NISPOM 2-28-2006” defines secure as follows: “The method of destruction must preclude recognition or reconstruction of the classified information or material.”
In this paper, we will be highlighting the three methods of destruction based on document destruction requirements. Less reputable destruction vendors may issue a certificate of destruction without being knowledgeable of the various required processes. When that occurs, where does the risk lie for the documents that may not be entirely destroyed?
1. Incineration:
 A typical incineration plant is pictured here.
A typical incineration plant is pictured here.
The image below shows a typical incineration process. The process will vary but the area of concern is the initial burn area below the feed. Here, not everything will burn 100%. There may be some “dropout” of unburned material that may be sent to a landfill.
Why should drop out be a concern? What if some of the unburned documents are literally blown away at the landfill? Or an employee of the incinerator or landfill could read the documents and then give the documents to the news/media or commit identity theft?
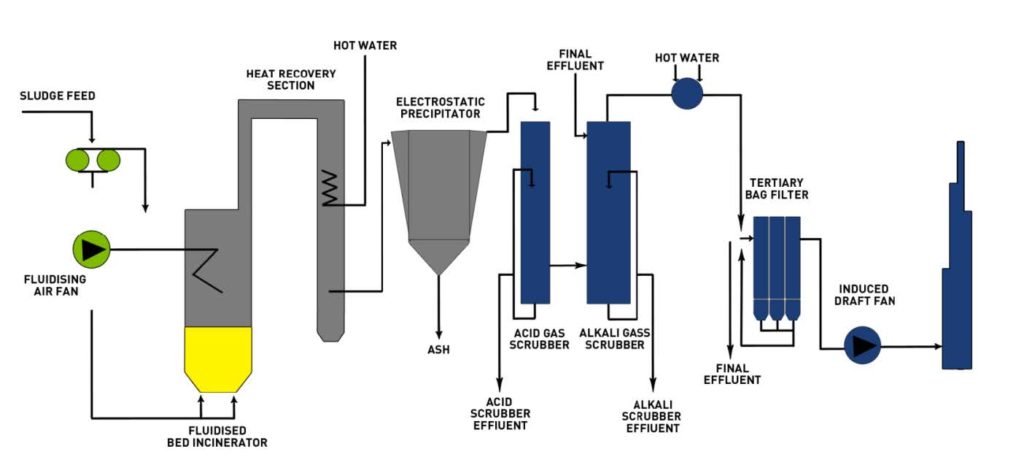
One risk management solution to unburned documents is to add to the specifications of secure destruction that any unburned documents shall be placed through the incineration process again. The second portion of this solution is to require a witness at the ash pit. The two items together can make incineration truly secure. A third party witness would also be more objective.
What we have not talked about is attempting to incinerate wet and/or frozen documents. Obviously, that makes matters many times harder. Evidence has shown that even hand feeding small batches at a time is not very effective. If incineration has to be used, plan on the extra effort and costs to monitor and recycle unburned documents back into the incinerator.
For very sensitive data it is best to pay for third party witnesses.
2. First Step-Secure Shredding of Paper:
This is the first stop on the road for the paper to be pulverized. Documents are securely received, shredded, baled and then sent to a paper mill for recycling/pulverizing.






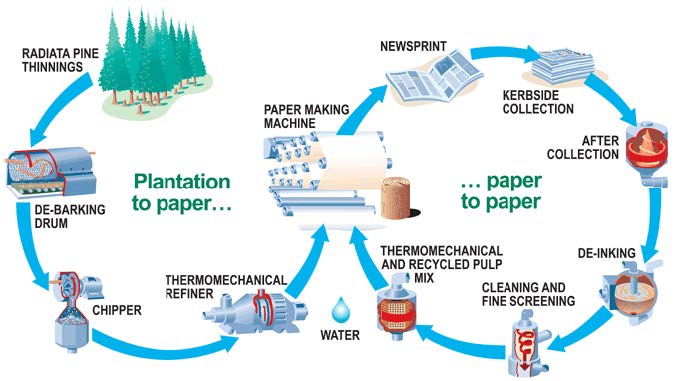
3. Pulverizing part of the recycling process:
Paper pulverizing is accomplished when a paper is mixed with wood chips or just other paper. The process turns everything into thick slurry called paper pulp. From the security standpoint, the digester accomplishes the task of meeting the definition of secure destruction: “The method of destruction must preclude recognition or reconstruction of the classified information or material.”
Secure Document Destruction
BMS CAT provides secure document destruction services that will meet many current industry standards. The following are our minimum standards:
- All BMS employees are trained to comply with the federal information protection laws.
- All employees have had a criminal background check, drug and alcohol screening and annual random re-verification.
- All areas are fenced in, locked and alarmed.
- Access to the shredding area is by controlled key access.
- The shredding area can contain an entire truckload off-loaded in a fenced-in area protected from the rest of the building.
- In this secure receiving area the shipment is received and verified.
- The load is fed into the shredder in this area.
- Video surveillance cameras are recording the entire shredding process.
- Upon completion of the shredding, the shredded material is baled and placed onto a trailer.
- The trailer is locked with a security seal.
- The trailer containing the securely shredded paper is transported directly to a paper mill to be placed into a vat to be converted into paper pulp to be recycled. There is no waste from this process.
- Witness certification can be provided upon request.
- Certification of Secure Destruction will be provided including some or all of the following information:
- The license number of the trailer delivering the documents.
- Seal number on the trailer.
- Name of the person cutting the seal and who their employer is.
- Name and date of the inventory manifest provided.
- The number of boxes and/or pallets.
- Weight is optional, but it does not track back to an inventory.
- Signature on the receiving manifest by the shredding facility.
- Chain of Custody: Chain of custody verification is accomplished with the Certificate of Destruction identifying the transport and receipt of the documents as outlined above.
Federal Standards Department of Defense NISPOM 2-28-2006
- BMS CAT secure document destruction via shredding and pulping meets the Federal Standards for SECRET and TOP SECRET level documents. The key in this area is that a cleared person must witness the destruction. Otherwise, the standard BMS CAT process will qualify.
- The standard states “The method of destruction must preclude recognition or reconstruction of the classified information or material.”
- Therefore, the shredding is a preparation process for pulping.